ENCLAVE is a confidential agent execution layer on 0G that splits AI agent logic into encrypted shards, runs them across separate TEE providers, and records all lifecycle events onchain to prevent any
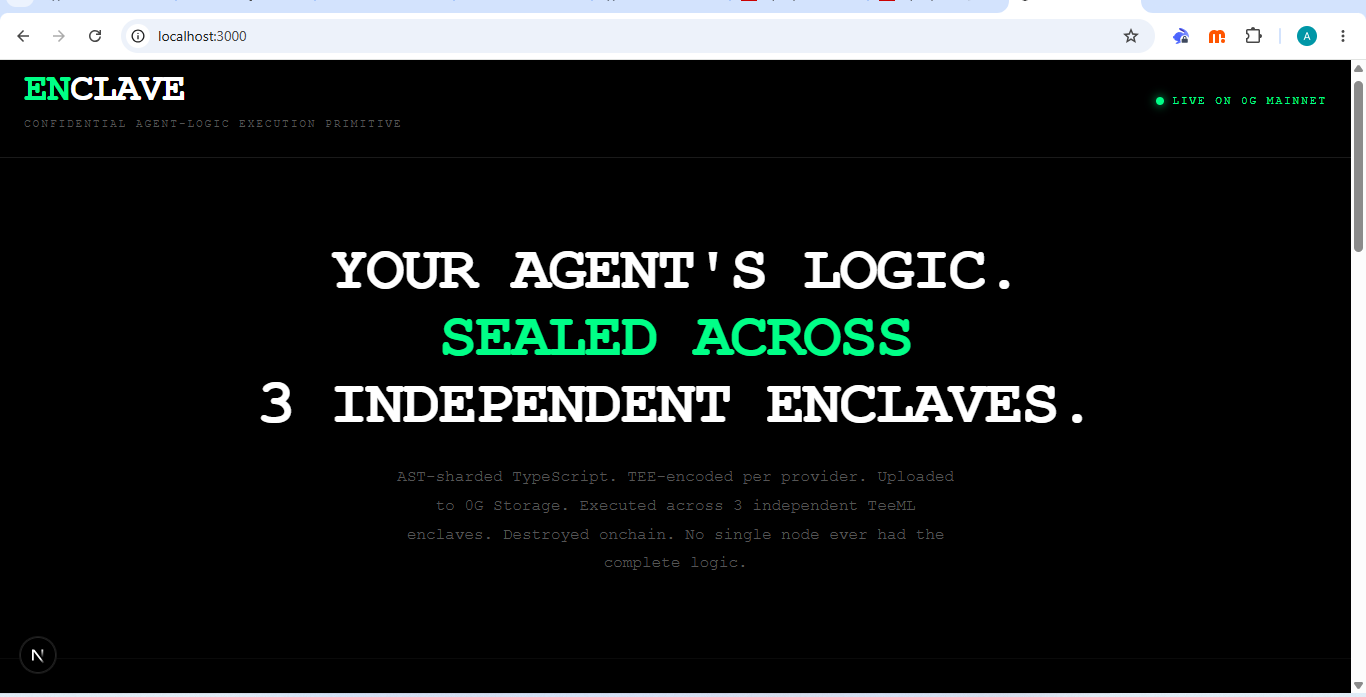

Confidential AI execution layer on 0G that lets developers run autonomous agents without exposing their full logic to any single compute provider.
ENCLAVE takes AI agents written in TypeScript and breaks them into smaller pieces (called shards) using an AST-based parser that splits code at function boundaries. Each shard is then encrypted using a session key generated inside a Trusted Execution Environment (TEE), meaning the key is created inside secure hardware and never exposed outside it.
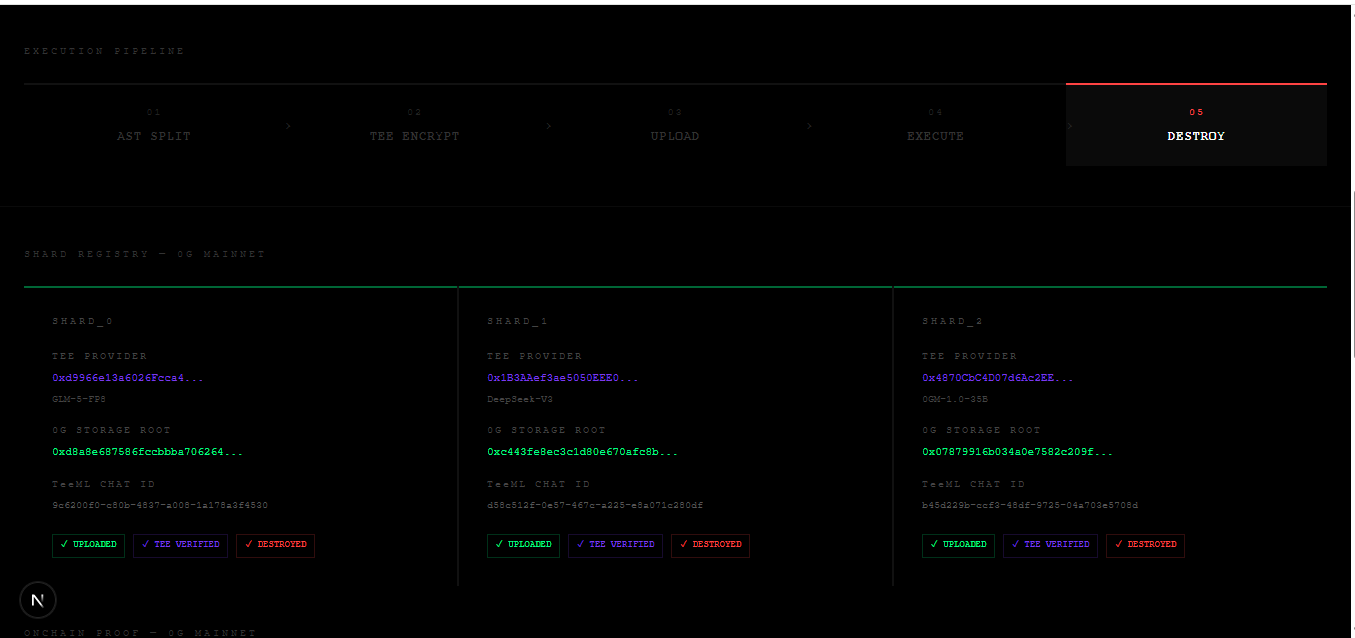
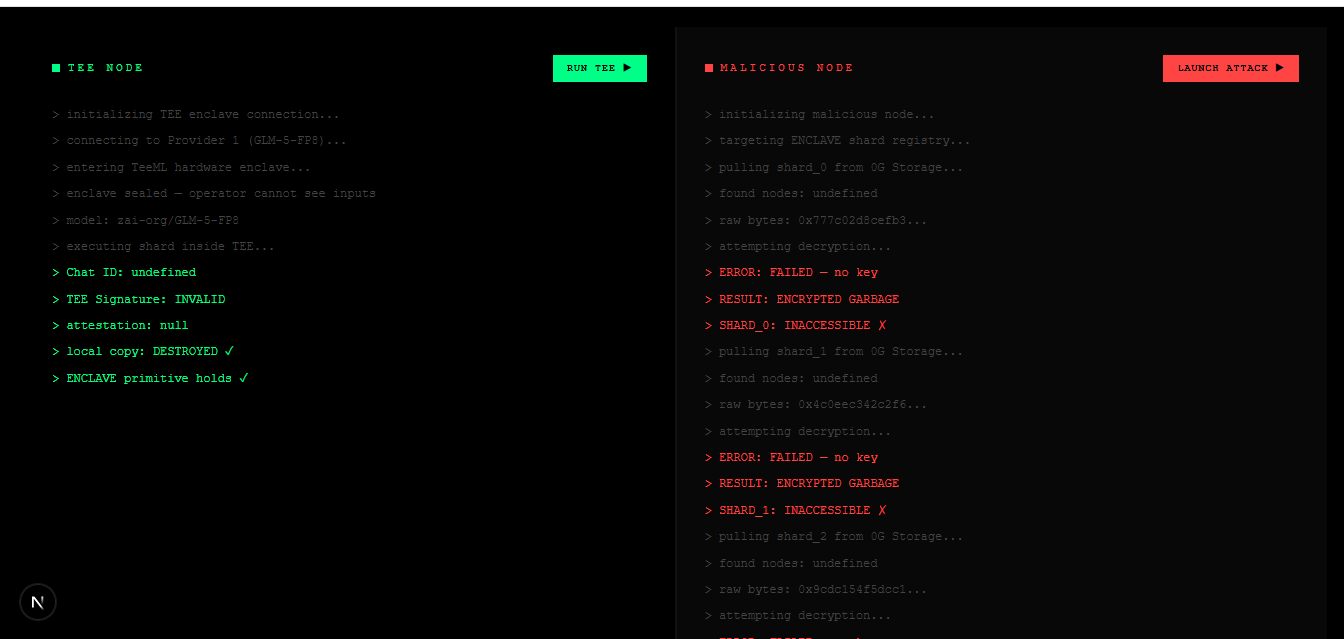
After encryption, the shards are distributed across multiple independent TeeML compute providers on 0G Compute. Each provider only receives one shard, so no single node can ever see or reconstruct the full agent. The shards are then executed inside isolated TEE environments, and all execution proofs are recorded onchain via a ShardRegistry contract on 0G Chain.
Encrypted shards are stored on 0G Storage with verifiable Merkle roots, and once execution is completed, both shards and session state are destroyed. This ensures the system is not just secure at rest, but also secure during execution and after execution.
ENCLAVE also includes a developer SDK called enclave-sdk-0g, which makes it very simple to use. Developers don’t need to understand all the infrastructure underneath—they can just install it and protect their agents with a single command:
npm install enclave-sdk-0g
Then they can use:
enclave.protect() → to shard, encrypt, and deploy an agent securely
enclave.verify() → to check execution proofs and onchain results
There is also a live dashboard: https://enclave-roan.vercel.app
It shows the full lifecycle of an agent in a simple interface—registration, shard creation, storage proofs, TEE execution, and destruction—so anyone can visually verify what’s happening without reading raw blockchain data.
Core components of ENCLAVE include:
AST Sharding Engine (splits agent logic)
TEE Session Key Generator (secure hardware-based encryption root)
Multi-Provider TeeML Execution Layer (isolated execution across nodes)
0G Storage Layer (encrypted shard storage with Merkle proofs)
ShardRegistry on 0G Chain (onchain lifecycle + attestations)
ENCLAVE SDK (enclave-sdk-0g) (developer interface)
Dashboard (visual verification layer)
In simple terms, ENCLAVE makes it possible to build AI agents that are confidential while running, verifiable onchain, and easy to deploy like a normal npm package, even in a decentralized and adversarial compute environment.
Key Infrastructure:
0G Storage (encrypted shard storage with Merkle roots)
0G Compute (TeeML execution across multiple providers)
0G Chain (onchain lifecycle + attestation recording)
0G AgentID
Built ENCLAVE from scratch during the hackathon — a confidential agent-logic execution primitive on 0G. Deployed the ShardRegistry smart contract on 0G Mainnet, integrated 0G Storage for encrypted shard persistence, and used 0G Compute TeeML for multi-enclave execution across three independent providers. Implemented AST-based semantic sharding middleware to split TypeScript agent logic at function boundaries and generate TEE-based session encryption keys inside secure enclaves.
Minted an ERC-7857 iNFT for agent identity and lifecycle provenance, and recorded all execution events, attestations, and destruction proofs onchain. Built and published an npm SDK (enclave-sdk-0g) exposing simple APIs like enclave.protect() and enclave.verify(), enabling one-command integration for developers. Also shipped a live Next.js dashboard for real-time visibility into shard lifecycle, storage roots, and onchain verification data.
All core components; compute, storage, chain, SDK, and dashboard are live and operational on 0G Mainnet.
Hackathon project on 0G APAC 2026. No funding raised yet.